A proxy server is an application that acts as an intermediate between the Internet and the users. Proxy servers have many different roles and one of them is providing extreme security and privacy. It keeps the user under protection by encrypting every data that passes the proxy server.
A user can choose and set up a proxy for additional security and to protect their personal details as a matter of privacy. It’s the middleman between the sender and the receiver which as a result separates direct contact. It provides a shared internet connection and clears cache data for efficient functioning.
How Proxy Servers Protect Your System From Hackers
We all are aware of internet security hackers. With less protection, there are higher possibilities for the hacker to steal information and sometimes even confidential ones. Basically, accessing the Internet without a proxy server is like going to a medieval fight without armor.
Hackers can easily break into computer systems to steal, change or destroy data. A proxy server comes in handy in such situations. It limits the number of personal details shown and uses extreme accuracy of personal accounts. It carefully monitors the web pages and functions as a firewall between a client and the server that is providing the source.
Many individuals that use torrenting platforms are often warned about their cybersecurity risks. Additionally, torrenting is banned in some countries of the world. If you do not want your ISP to figure out whether you are torrenting or not, please use a proxy server that can help you evade monitoring. To know more about how you can protect your digital footprint and keep cybercriminals at bay, click here.
Proxy and IP
Proxy Server has several benefits such as hackers won’t be able to access a user's Internet Protocol (IP) address which means they will be unable to invade their computer or internet. A proxy can maintain the structure of the local network by examining the data which is being entered and taken down from the system. This kind of proxy is known as Anonymous Proxy.
An IP address is an essential element of the Internet because it gives a unique identity to your system. But in case you had no clue, there are higher risks involving the IP.
A proxy server disables the option of showing personal IP. This acts as the best solution because, without the personal IP address, hackers do not have the means of approach to personal information, data, passwords, or other files. A proxy server acts as an extra layer of protection as it enhances security.
Why Is There A Need to Hide the IP Address You’re Using?
When our system has public IP, it can be used to access massive amounts of data and information that are stored inside the computer. It can easily display the person's location crystal clear (street, city, state, and country). One of the main reasons to hide IPs is to safeguard our systems from hacking and phishing.
It's better not to take a chance on exposing your private information. A precautionary measure would be the smartest move here. It's a good idea to remain anonymous online.
For instance, we are always excited to use free Wi-Fi when we are in a public area. To have the privilege of using the available resource, one must provide their mobile number to access the internet. By using a proxy, we can prevent ourselves from being tracked later on.
Role of Proxy Server in Privacy and Security
It is like a substituting agent when the user wants to remain anonymous and hide the details and information from the people on the internet. When you decide on using the proxy, you will be the only one to know the IP address of your server.

However, your original IP address can still be identified by the operator or the owner of the proxy server. We cannot say anything with certainty. This is how it basically functions:
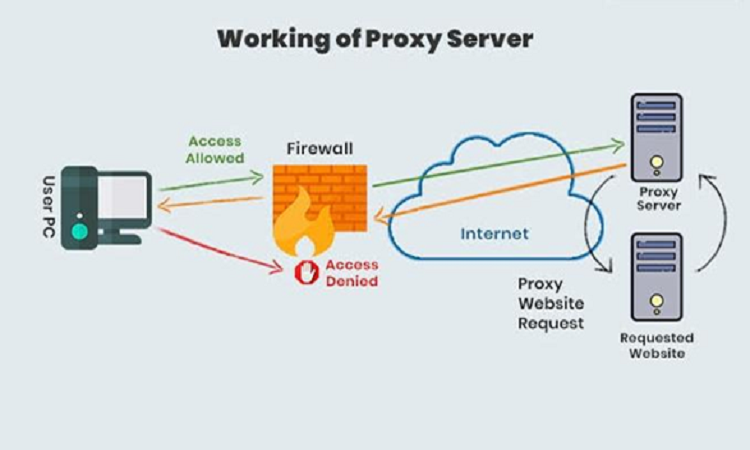
- When a client comes in and requests to any website then the request first directly reaches the attached proxy server.
- To shield the personal data of the user, the proxy changes the IP address so that the actual IP address which would have been provided during the purchase is not revealed to the website.
- Then it gathers all the responses from the site and forwards the obtained result to the client.
- By this, there is no way possible to have access to the server. So, they also can’t track down the location of the person who is.
- It receives traffic from the request sender and responds to it accordingly after filtration.
When you have access to a proxy server, it is difficult for the other networks to identify your activities, thus it's really safe and secure. You can share confidential information without the fear of getting hacked. It also enhances privacy and the smooth functioning of your system.
The Socket Secure Protocol (SOCKS) serves as an authentication protocol to make sure that the ones with an authentication key will be granted access. A SOCKS5 proxy is the latest version of the protocol with 3 authentication steps for enhanced security measures.
You can use a static residential proxy, a special kind of proxy server, to access the Internet from a real IP address. This kind of proxy allows you to access region-restricted content while still hiding your IP address. There are a few more variations of proxy servers and each one of them can be used to improve your privacy and security.
A proxy server plays a huge role in improving the security and privacy of your network. You can’t just rely on pre-installed firewalls to protect confidential information from hackers. You have to upgrade your security and protect your data using proxy servers.
NOTE: A free proxy server offers less protection and security for your data. It is highly suggested to subscribe to a proxy provider to make sure that all of your information is encrypted and secured from end to end.
Conclusion
When it comes to privacy and security, proxy servers are the single most effective solution to the problem. These third-party servers mask your IP address with a new one - just like covering an old paint with a new one. This prevents your original IP address (and your data) from being tracked by malicious acts.
A proxy server’s mandate is to serve as a primary layer of protection against potential hackers and information leaks. If there’s anything fishy that’s happening, the service provider will let you know as soon as possible to prevent any data and information breaches.